There are different types of cyber attacks, which vary according to the objectives to be achieved and the technological and contextual scenarios:
Among the most common attacks, in recent times, there are attacks for economic purposes and attacks for data flows. After analyzing the Man in the Middle, Malware and Phishing, in recent weeks, today we see thedrive-by attack.
Those who carry out the cyber attack, alone or in groups, are called Chippers
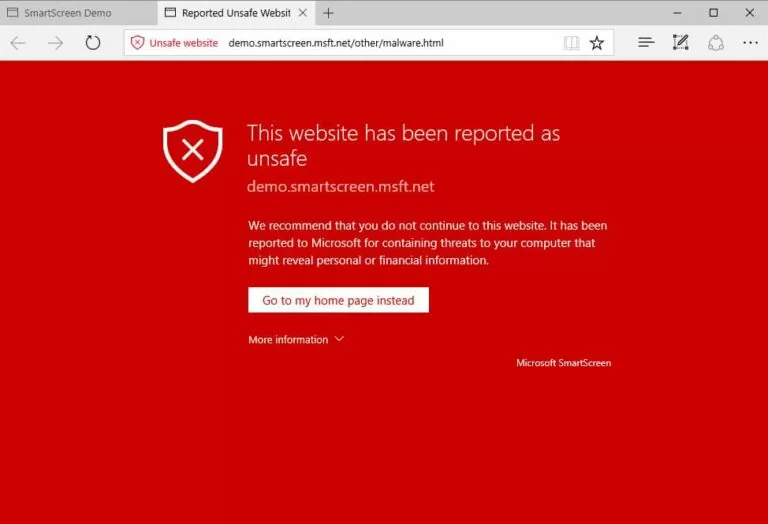
Drive-by download attacks are a common method of spreading malware. Hackers search for insecure websites and insert a malicious script into the HTML or PHP code of one of the pages. This script could install malware directly on someone's computer visiting the site, or it could redirect the victim to a hacker-controlled site. Drive-by downloads can occur when you visit a website or view an email message or pop-up window. Unlike many other types of cybersecurity attacks, a drive-by does not rely on the user doing something to actively activate the attack - no need to click a download button or open an email attachment. harmful to get infected. A drive-by download can exploit an app, operating system, or web browser that contains security holes due to failed updates or a lack of updates.
To protect yourself from drive-by attacks, you need to keep your browsers and operating systems up to date and avoid websites that may contain malicious code. Stick to the sites you normally use - but be aware that these sites can also be hacked. Don't keep too many unnecessary programs and apps on your device. The more plug-ins you have, the more vulnerabilities there are that can be exploited by drive-by attacks.
If you have suffered an attack and need to restore normal functioning, or if you simply want to see clearly and understand better, or want to prevent: write to us at rda@hrcsrl.it.
You might be interested in our Man in the Middle post
If you have suffered an attack and need to restore normal operation, or if you simply want to see clearly and understand better, or want to prevent: write to us at rda@hrcsrl.it.
You might be interested in our Malware Post
While drive-by attacks are potentially very dangerous, you can do a lot to prevent them by minimizing the risks and keeping your data, money and… dignity safe.
You absolutely must get an effective and reliable antivirus software
If your budget is tight, you can find numerous free antivirus online
It is the fundamental process for measuring your company's current level of security.
To do this it is necessary to involve an adequately prepared Cyber Team, able to carry out an analysis of the state in which the company finds itself with respect to IT security.
The analysis can be carried out synchronously, through an interview carried out by the Cyber Team or
also asynchronous, by filling in a questionnaire online.
We can help you, contact the HRC srl specialists by writing to rda@hrcsrl.it.
More than 90% of hacker attacks start with employee action.
Awareness is the first weapon to combat cyber risk.
This is how we create "Awareness", we can help you, contact the HRC srl specialists by writing to rda@hrcsrl.it.
Corporate data is of enormous value to cybercriminals, which is why endpoints and servers are targeted. It is difficult for traditional security solutions to counter emerging threats. Cybercriminals bypass antivirus defenses, taking advantage of corporate IT teams' inability to monitor and manage security events around the clock.
With our MDR we can help you, contact the HRC srl specialists by writing to rda@hrcsrl.it.
MDR is an intelligent system that monitors network traffic and performs behavioral analysis
operating system, identifying suspicious and unwanted activity.
This information is transmitted to a SOC (Security Operation Center), a laboratory manned by
cybersecurity analysts, in possession of the main cybersecurity certifications.
In the event of an anomaly, the SOC, with a 24/7 managed service, can intervene at different levels of severity, from sending a warning email to isolating the client from the network.
This will help block potential threats in the bud and avoid irreparable damage.
The dark web refers to the contents of the World Wide Web in darknets that can be reached via the Internet through specific software, configurations and accesses.
With our Security Web Monitoring we are able to prevent and contain cyber attacks, starting from the analysis of the company domain (e.g.: ilwebcreativo.it ) and individual e-mail addresses.
Contact us by writing to rda@hrcsrl.it, we can prepare a remediation plan to isolate the threat, prevent its spread, and defiwe take the necessary remediation actions. The service is provided 24/XNUMX from Italy
CyberDrive is a cloud file manager with high security standards thanks to the independent encryption of all files. Ensure the security of corporate data while working in the cloud and sharing and editing documents with other users. If the connection is lost, no data is stored on the user's PC. CyberDrive prevents files from being lost due to accidental damage or exfiltrated for theft, be it physical or digital.
The smallest and most powerful in-a-box datacenter offering computing power and protection from physical and logical damage. Designed for data management in edge and robo environments, retail environments, professional offices, remote offices and small businesses where space, cost and energy consumption are essential. It does not require data centers and rack cabinets. It can be positioned in any type of environment thanks to the impact aesthetics in harmony with the work spaces. «The Cube» puts enterprise software technology at the service of small and medium-sized businesses.
Contact us by writing to rda@hrcsrl.it.
You might be interested in our Man in the Middle post
Ercole Palmeri: Innovation addicted
[ultimate_post_list id=”12982″]
Google DeepMind is introducing an improved version of its artificial intelligence model. The new improved model provides not only…
Laravel, famous for its elegant syntax and powerful features, also provides a solid foundation for modular architecture. There…
Cisco and Splunk are helping customers accelerate their journey to the Security Operations Center (SOC) of the future with…
Ransomware has dominated the news for the last two years. Most people are well aware that attacks…
An ophthalmoplasty operation using the Apple Vision Pro commercial viewer was performed at the Catania Polyclinic…
Developing fine motor skills through coloring prepares children for more complex skills like writing. To color…
The naval sector is a true global economic power, which has navigated towards a 150 billion market...
Last Monday, the Financial Times announced a deal with OpenAI. FT licenses its world-class journalism…